White paper
Research and Development (R&D) Department – Daw Alfada Company
Abstract
The oil and gas industry, a cornerstone of the global economy, is increasingly reliant on digital
technologies, making it a prime target for cyberattacks. Threat actors exploit vulnerabilities in
critical infrastructure to disrupt operations, cause financial losses, and pose environmental and
safety risks. This white paper examines the evolving threat landscape, highlights key
vulnerabilities, and proposes actionable strategies to mitigate these risks. By understanding
these challenges and adopting proactive measures, organizations in the sector can enhance
operational resilience and safeguard their assets.
Introduction
1.1 The Importance of the Oil and Gas Sector
The oil and gas industry plays a vital role in fueling the global economy, providing energy for transportation, heating, electricity, and industrial processes. The industry’s critical infrastructure spans exploration, production, transportation, refining, and distribution—a complex ecosystem increasingly managed through digital and automated systems.
1.2 Growing Reliance on Digital Technologies
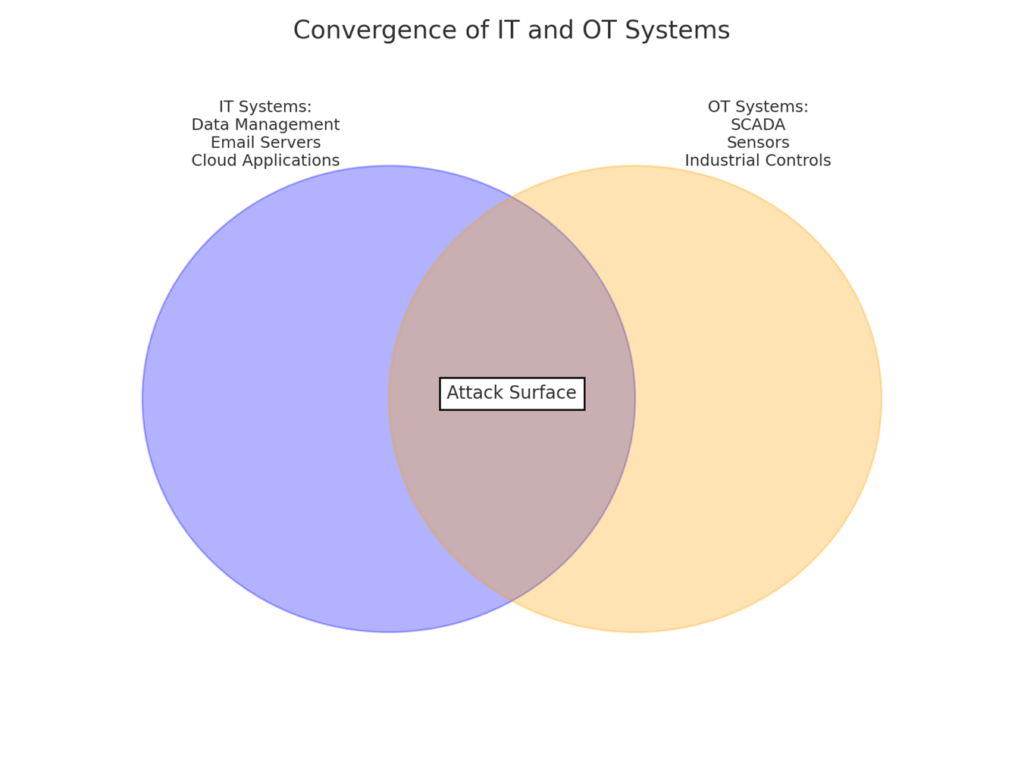
The integration of Information Technology (IT) with Operational Technology (OT) has revolutionized efficiency and monitoring in the sector. Technologies such as the Internet of Things (IoT), Artificial Intelligence (AI), and cloud computing are widely adopted to optimize operations. However, this digital transformation also introduces new vulnerabilities.
1.3 Objectives of the White Paper
- To provide a detailed analysis of the current cyber threat landscape.
- To identify vulnerabilities unique to the oil and gas sector.
- To propose strategies and technologies for effective cybersecurity measures.
- The Current Threat Landscape
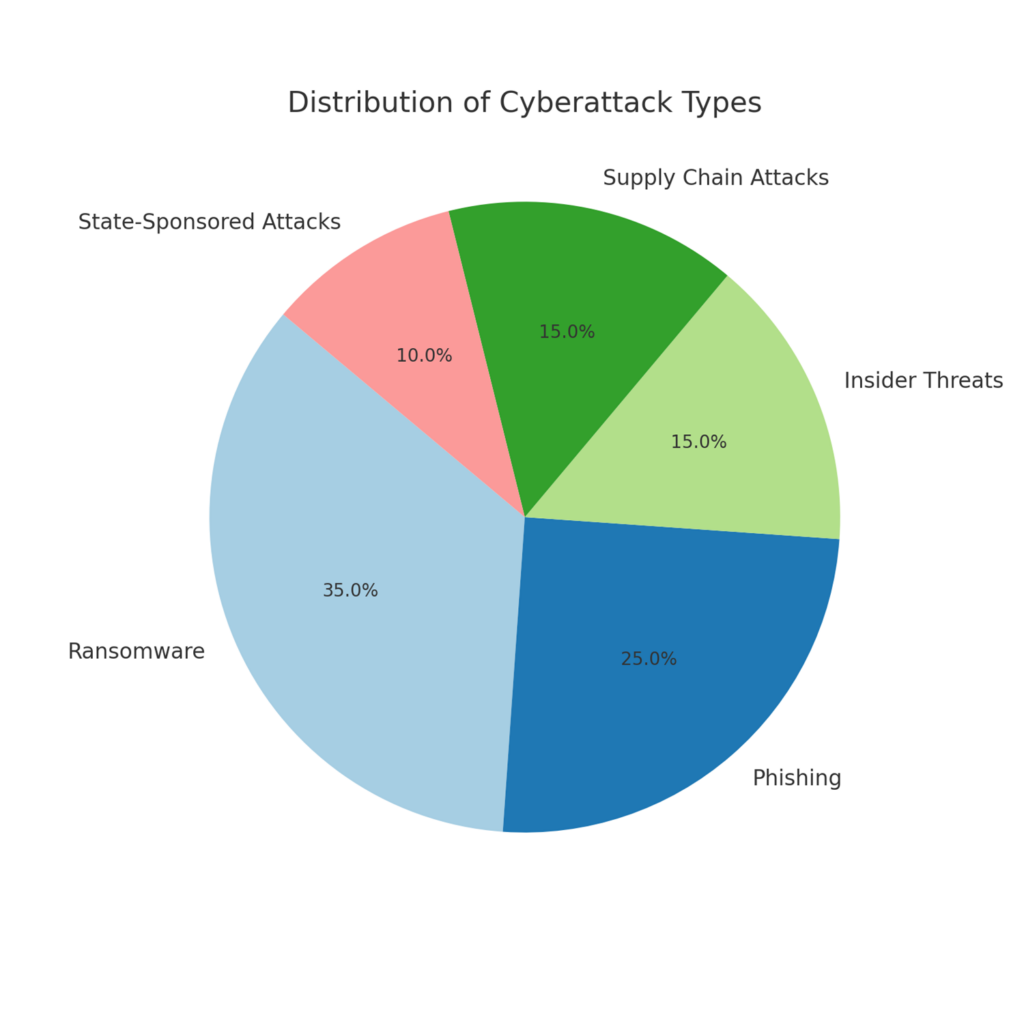
2.1 Types of Cyber Threats
- Ransomware Attacks: High-profile incidents, such as the Colonial Pipeline attack in 2021, demonstrated the devastating impact of ransomware, causing fuel shortages and financial losses.
- Phishing and Social Engineering: Attackers often exploit human vulnerabilities, targeting employees to gain access to critical systems.
- Insider Threats: Disgruntled employees or contractors may intentionally or inadvertently compromise security.
- Supply Chain Attacks: Weaknesses in third-party vendors or suppliers are exploited to infiltrate networks.
- State-Sponsored Attacks: Geopolitical tensions have escalated targeted cyberattacks by nation-states, aiming to disrupt critical infrastructure.
2.2 Impact of Threats
- Financial Losses: Average costs of breaches in the sector range from $4.45M to $4.65M.
- Operational Downtime: Cyberattacks can halt production and disrupt supply chains.
- Environmental Risks: Breaches can lead to leaks, spills, or explosions, posing severe environmental hazards.
2.3 Statistical Trends
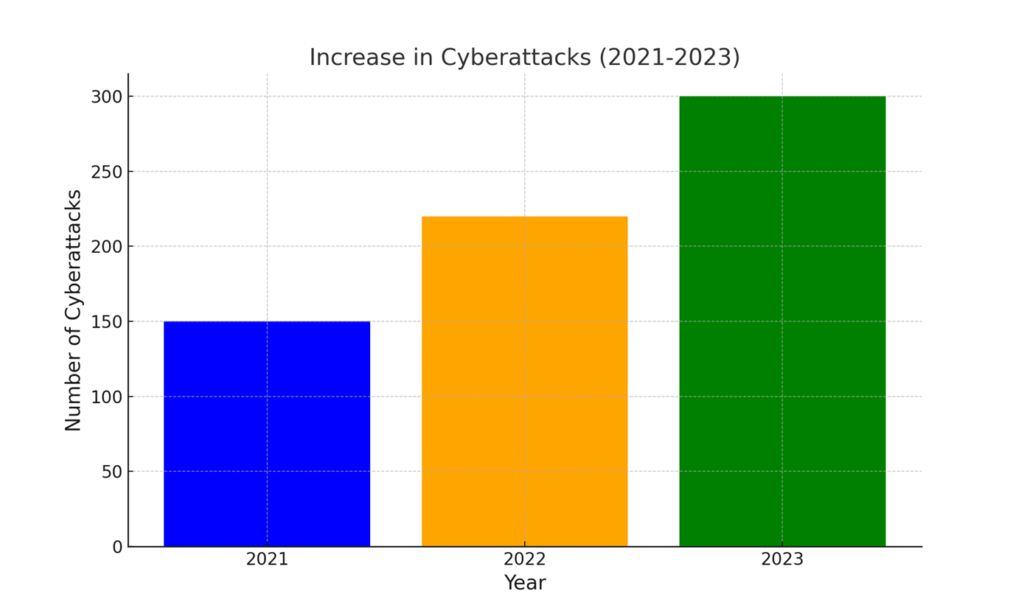
|
Metric |
2021 |
2022 |
2023 |
|
Number of cyberattacks in the sector |
150 |
220 |
300 |
|
Average cost of a data breach |
$4.24M |
$4.45M |
$4.65M |
|
Percentage of ransomware victims |
35% |
40% |
45% |
3.Vulnerabilities in the Oil and Gas Sector
3.1 Legacy Systems
Many companies continue to rely on aging systems that lack modern security protocols, making them susceptible to exploitation.
3.2 Convergence of IT and OT
The integration of IT (enterprise systems) and OT (control systems) introduces interconnected vulnerabilities, creating potential entry points for attackers.
3.3 Lack of Cybersecurity Awareness
Insufficient training among employees and contractors increases the risk of successful phishing or social engineering attacks.
3.4 Dependence on Third-Party Vendors
A significant portion of the sector’s operations relies on external vendors, making supply chain security critical.
- Case Studies
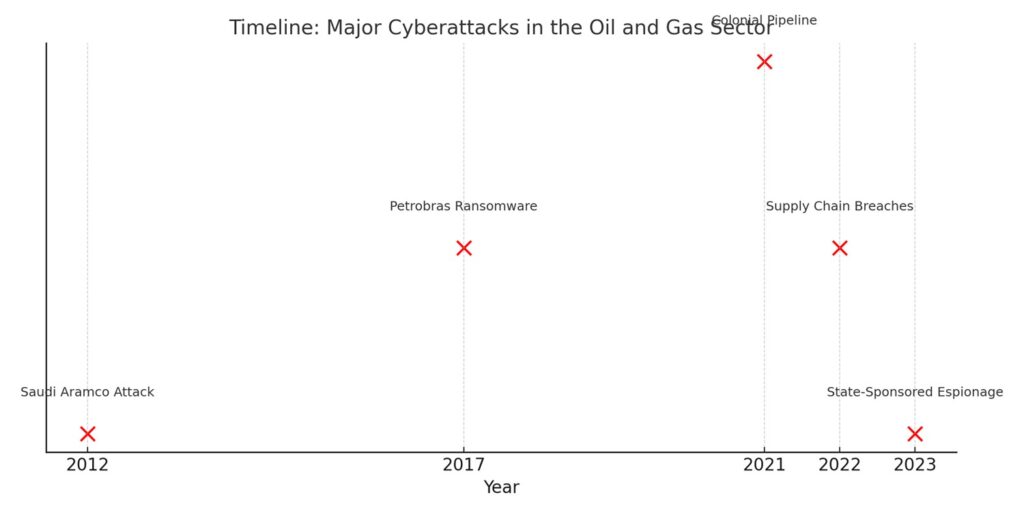
4.1 Colonial Pipeline Attack (2021)
- Overview: A ransomware attack disrupted fuel supply across the U.S.
- Impact: Financial losses exceeding $4.4M in ransom payments and significant reputational damage.
- Lessons Learned: Importance of network segmentation and robust backup systems.
4.2 Saudi Aramco Cyberattack (2012)
- Overview: State-sponsored malware (Shamoon) erased data from 30,000 computers.
- Impact: Operational disruption and financial losses.
- Lessons Learned: The need for endpoint security and disaster recovery plans.
4.3 Recent Attacks (2022-2023)
Here’s a detailed section covering recent attacks (2022-2023) with an emphasis on cloud vulnerabilities, OT systems, and IoT devices:
4.3 Recent Attacks (2022-2023)
The past two years have seen a significant rise in targeted cyberattacks against the oil and gas sector, particularly exploiting cloud infrastructure, operational technology (OT) systems, and Internet of Things (IoT) devices. These incidents highlight the rapidly evolving threat landscape and underscore the need for robust cybersecurity measures.
- Cloud Vulnerabilities
Attack on Global Energy Provider (2022)
- Incident: A cloud misconfiguration in the energy provider’s hybrid infrastructure allowed attackers to exploit privileged access management tools, exposing sensitive operational data.
- Impact: The breach disrupted supply chain operations for several weeks and cost the company approximately $12 million in direct recovery and compliance penalties.
- Lessons Learned:
- Continuous monitoring of cloud environments is essential.
- Secure cloud configurations and robust identity management practices are critical.
- OT Systems
OT Ransomware Attack on Refinery (2023)
- Incident: A ransomware group infiltrated the OT systems of a major refinery using spear-phishing emails targeted at employees with OT network access.
- Impact: The attack halted production for five days, causing financial losses estimated at $22 million. Additionally, it delayed the shipment of fuel to distributors.
- Lessons Learned:
- Isolate OT networks from IT systems with strict segmentation.
- Implement network monitoring tools to detect anomalies in OT traffic.
- IoT Devices
Compromise of IoT Sensors in Pipeline Monitoring (2023)
- Incident: Cybercriminals exploited outdated firmware in IoT pressure sensors monitoring a natural gas pipeline. The breach allowed manipulation of sensor readings, creating operational chaos.
- Impact: The incident disrupted pipeline flow for 48 hours and caused reputational damage, with regulatory investigations launched into IoT security policies.
- Lessons Learned:
- Regular updates and patches for IoT devices are crucial.
- Conduct vulnerability assessments on IoT networks and devices.
Key Takeaways from Recent Incidents
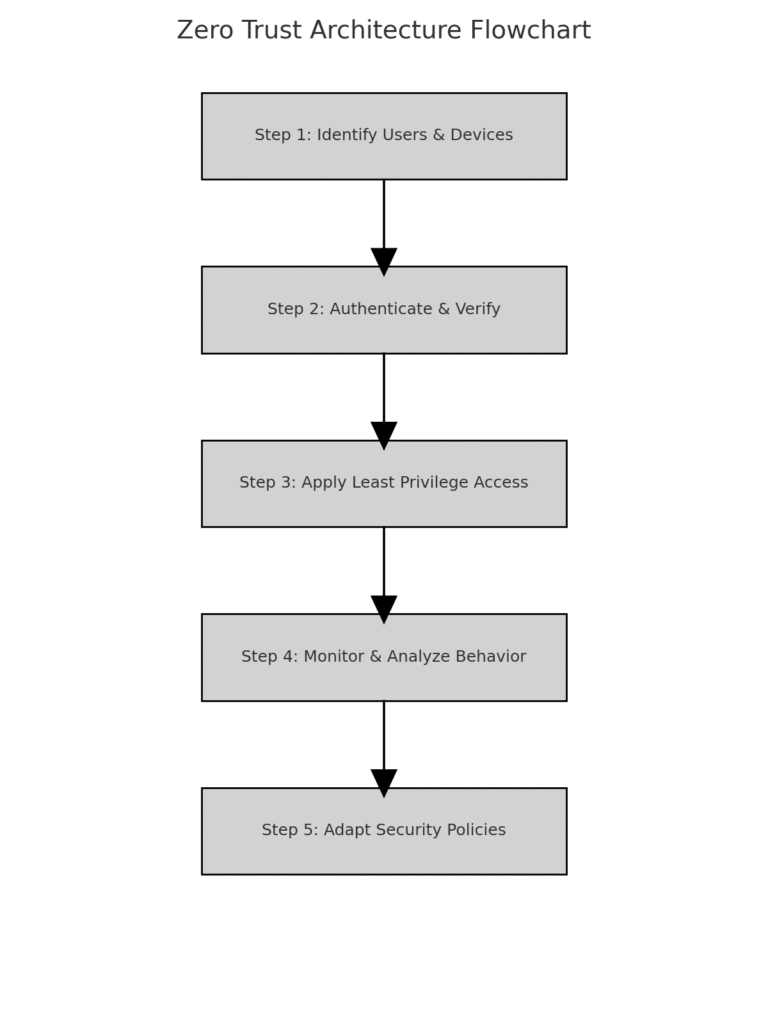
- Cloud Security Gaps: Organizations must implement Zero Trust policies to minimize unauthorized access and invest in advanced security solutions like cloud workload protection platforms (CWPP).
- OT Systems as Prime Targets: Enhanced training for OT staff, intrusion detection systems, and physical security can reduce risks.
- IoT Device Protection: Device hardening, firmware patching, and network encryption are fundamental to securing IoT ecosystems.
A table or infographic summarizing the incidents, impacts, and lessons learned for quick reference:
|
Attack Type |
Year |
Target |
Impact |
Lessons Learned |
|
Cloud Misconfiguration |
2022 |
Energy Provider |
$12M in losses, data breach |
Continuous monitoring, secure cloud configurations |
|
OT Ransomware |
2023 |
Refinery |
$22M in losses, downtime |
Network segmentation, OT traffic anomaly detection |
|
IoT Device Exploitation |
2023 |
Pipeline monitoring sensors |
Pipeline disruption, fines |
Firmware updates, IoT vulnerability assessments |
5.Emerging Trends in Cyber Threats
5.1 AI-Powered Attacks
Sophisticated attackers leverage AI to automate reconnaissance and enhance attack success rates.
5.2 Cloud Vulnerabilities
The widespread migration to cloud services introduces risks such as misconfigurations and unauthorized access.
5.3 Geopolitical Tensions
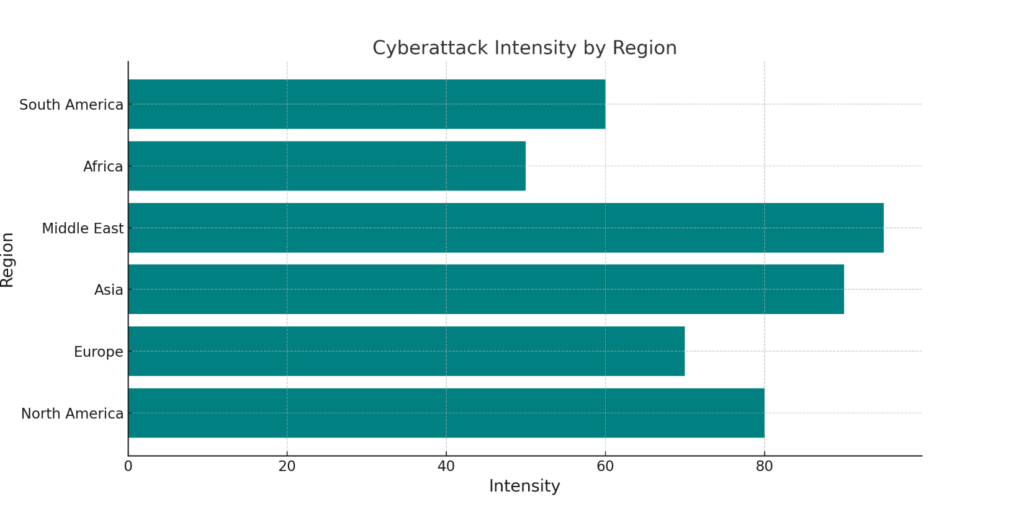
State-sponsored attacks increasingly target critical infrastructure as geopolitical conflicts intensify.
6.Mitigation Strategies
6.1 Implementing Zero Trust Architecture
Adopt strict access controls, continuous monitoring, and multi-factor authentication to reduce risks.
6.2 Regular Security Audits and Training
Conduct frequent vulnerability assessments and educate employees on cybersecurity best practices.
6.3 Technology Investments
Deploy advanced firewalls, intrusion detection systems, and AI-driven threat detection tools.
6.4 Collaboration with Industry and Government
Collaboration between the private sector and government in the oil and gas industry is crucial for strengthening cybersecurity defenses and sharing valuable threat intelligence. Here are some key points on how such partnerships can be structured to enhance collective defenses:
- Public-Private Partnerships (PPP):
- Joint Cybersecurity Task Forces: Establish task forces that include representatives from both the government and private companies. These task forces can work together to share intelligence, best practices, and lessons learned from previous cyber incidents.
- Cybersecurity Frameworks: Governments can encourage the oil and gas industry to adopt national or international cybersecurity standards and frameworks, such as the NIST Cybersecurity Framework or ISO 27001, to ensure a unified approach to security.
- Threat Intelligence Sharing:
- Information Sharing and Analysis Centers (ISACs): Create industry-specific ISACs where organizations can voluntarily share threat data, attack indicators, and tactics, techniques, and procedures (TTPs) to improve situational awareness.
- Real-time Threat Monitoring: Governments and private companies can collaborate on setting up real-time threat monitoring systems, providing a rapid response capability in the event of cyberattacks or other security incidents.
- Incident Response and Coordination: Establish a clear protocol for coordinating responses to cyberattacks, with both public and private sector entities working together to contain and mitigate the effects.
- Cybersecurity Research and Development:
- Joint R&D Initiatives: Government funding and incentives can support joint research initiatives with the private sector to develop next-generation cybersecurity solutions tailored to the specific needs of the oil and gas industry.
- Critical Infrastructure Protection: Focus on developing cybersecurity technologies that can specifically safeguard critical infrastructure in the oil and gas sector, such as pipeline monitoring systems, control systems, and industrial control networks.
- Training and Awareness Programs:
- Cross-sector Training: Both government agencies and private companies can collaborate on workforce development programs, offering cybersecurity training and simulations for employees across various sectors of the oil and gas industry.
- Public Awareness Campaigns: Governments and industry associations can launch public awareness campaigns aimed at educating employees, from executives to field workers, on cybersecurity risks and best practices.
- Regulation and Compliance:
- National Cybersecurity Legislation: Governments can create or update regulations requiring private oil and gas companies to implement strong cybersecurity measures, conduct regular audits, and report any incidents in a timely manner.
- Compliance Incentives: Offer incentives for companies that demonstrate a commitment to cybersecurity through certifications, risk assessments, and investment in resilient systems.
- Information Exchange Platforms:
- Secure Communication Channels: Set up secure platforms for real-time communication between government agencies, industry leaders, and security researchers to ensure that sensitive threat intelligence can be exchanged quickly and confidentially.
By fostering collaboration between the public and private sectors, the oil and gas industry can develop more robust defenses, improve resilience to cyber threats, and ensure better overall protection of critical infrastructure.
- Conclusion
The oil and gas sector’s increasing reliance on digital technologies demands a proactive approach to cybersecurity. By addressing vulnerabilities, staying informed about emerging threats, and implementing robust mitigation strategies, the industry can protect its critical infrastructure and ensure operational resilience in an era of escalating cyber risks.
- References
- IBM’s Cost of a Data Breach Report.
- Cybersecurity reports from FireEye, CrowdStrike, and McAfee.
- Studies by the World Economic Forum and the International Energy Agency (IEA).



